How We Found the Vulnerability
While testing our OT security product StationGuard and StationScout, we noticed some unusual system behavior. Specifically, the system crashed when we sent large data packets, known as Jumbo Frames, to the device. After thorough investigation, we identified the cause: a problem with Intel's IGB driver, a piece of software that is responsible for default network communication on many Linux systems.
How This Linux Vulnerability Can Be Exploited
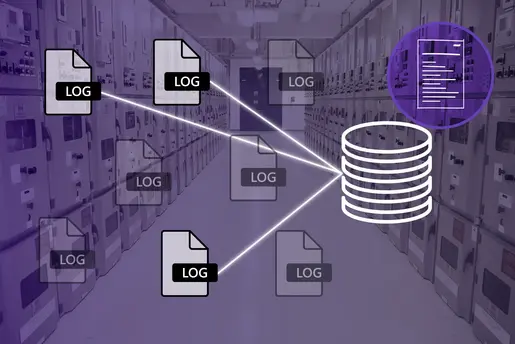
Attackers don't need malware to exploit this vulnerability (CVE-2023-45871), they can simply send these large data packets (Jumbo Frames) to vulnerable linux devices, potentially crashing the entire system within seconds. This doesn't require any special software to be running on the device, making any system using this network driver susceptible. A specific setting (rx-all flag) must be enabled, allowing the system to accept all types of data packets, even corrupted and oversized ones.
What are Jumbo Frames?
Jumbo Frames are larger-than-normal data packets used in network communications. Typically, Ethernet packets are up to 1500 bytes in size, but Jumbo Frames can be up to 9000 bytes. These larger packets are quite common and can improve bandwidth efficiency by sending more data at once.
The Impact
The oversized frames can overflow the memory allocated for the network adapter and spill into the system's main memory. Since the network driver is part of the system's core software (the Kernel), this overflow can cause significant issues, including the possibility of remote code execution. This means an attacker could potentially scan and take control of the entire system.
What to Do Next for Your Security
We have released updates for StationGuard (version 2.30.0092) and StationScout (version 2.30.0066) to fix this vulnerability. We strongly recommend that all customers update to the latest versions. Intel advises all users of the IGB driver to update their Linux systems to version 6.5.3 to mitigate this issue.
Lessons Learned
This incident shows that even trusted and widely-used software can have hidden vulnerabilities. We recommend that you always investigate unusual system behavior, as it might reveal new vulnerabilities that haven't been officially recognized yet.
For more information about this issue, visit: NVD - CVE-2023-45871 (nist.gov).
Special thanks to our colleagues Manfred Rudigier, Thomas Hotz, Jodok Simma, and Eric Heindl for discovering, reporting, and fixing this vulnerability. This vulnerability was reported to Intel on July 31, 2023, and is fixed in the latest driver version: Linux Kernel Changelog 6.5.3. For further information about the IGB driver, see the Linux Kernel documentation.