Minimizing cybersecurity vulnerabilities at the hardware level
Welcome to the 8th episode of our Energy Talks miniseries, Cybersecurity in the Power Grid, in which we provide a 360-degree view of how power grids can best safeguard their infrastructures from cyber attacks.
This episode investigates why, in addition to software, hardware devices must be secured against cyber threats.
OMICRON hardware developer Marcel Ströhle describes how hardware cybersecurity is crucial to overall system security because hardware devices are another potential attack vector that can be easily neglected. Through examples of actual hardware attacks, he highlights how important proper cybersecurity is for your hardware applications and offers tips to ensure it.
Marcel shares his experiences securing hardware devices and describes how he and his team have developed reliable and robust hardware technology, such as the MBX2 mobile device.
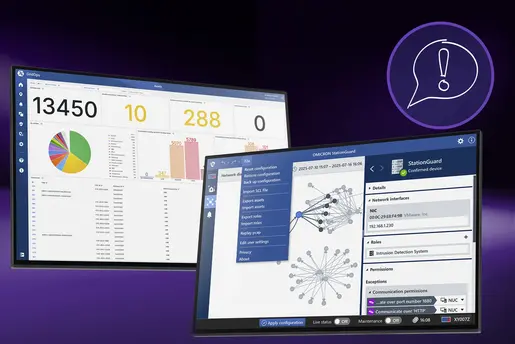
Learn more about OMICRON’s approach to cybersecurity in power grids.
Listen to our podcastHere Are The Key Topics from This Episode
Importance of Hardware Cybersecurity: In this part of the series, Scott Williams and Marcel Ströhle discuss the significance of hardware cybersecurity in addition to software security. Marcel explains the necessity of securing hardware components due to their foundational role and potential vulnerabilities.
Real Life Examples: Scott and Marcel discuss real-life scenarios to highlight the importance of hardware cybersecurity. Marcel uses the Stuxnet incident as a key example, where a USB stick with malware severely damaged Iranian nuclear centrifuges.
Navigating Cybersecurity Layers: They discuss the distinctions between hardware, firmware, and software in cybersecurity. Marcel explains that hardware includes application-specific chips (ASICs) and microcontrollers, which are defined by programming and firmware respectively.
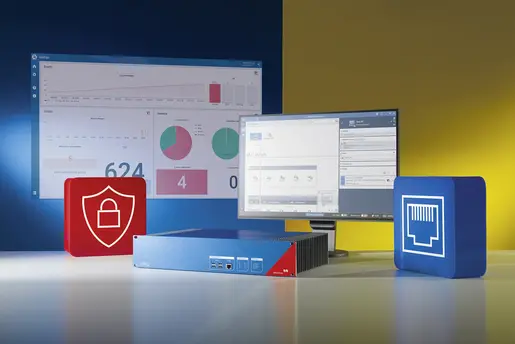
OMICRON’s MBX Platform and Future Trends: Scott and Marcel delve into the advanced security measures embedded in OMICRON's MBX platform, highlighting strategies like interface disabling and industrial-grade component selection.
Scott Williams: Hello everyone! Welcome to Part 8 of our miniseries "Cybersecurity in the Power Grid". Today, we are diving into hardware cybersecurity. We often focus on software security, but it's equally important to secure hardware devices against cyber threats. Joining me is Marcel Ströhle, a hardware developer at OMICRON, who will share his insights on this topic. Marcel, thank you for joining us for this episode of Energy Talks.
Marcel Ströhle: Thanks for having me. I've been looking forward to this chat.
Scott Williams: Marcel, could you start by telling us a bit about yourself? I understand you've been working on a new mobile platform at OMICRON called MBX2. What can you tell us about this platform, and what inspired you to pursue hardware development?
Marcel Ströhle: Sure. The MBX2 is an update to our existing MBX platform, utilizing new components and incorporating feedback from our customers. About myself, I've always been fascinated by puzzles and enjoyed taking apart technical things since I was a child. We had a good electronics school nearby, which made it easy to pursue this field. A friend who has worked at OMICRON for 15 years inspired me to join the company. Additionally, I've been into computers since my teenage years, building and optimizing them, which gave me a strong foundation in hardware.
Scott Williams: That's a great background. Let's dive into the topic. Many people think of cybersecurity solely in terms of software. Why should we also be concerned about the security of hardware components?
Marcel Ströhle: Hardware is the foundation upon which everything else is built. Any vulnerability in the hardware can be exploited, providing a gateway to critical components like drivers and the kernel. Modern computers come with various interfaces, such as Bluetooth and Wi-Fi, which might not be obvious to the user but can be exploited if not properly secured. The complexity of hardware design also adds to the challenge, as more transistors and advanced features increase the potential for security loopholes.
Scott Williams: Can you give us some examples of how hardware vulnerabilities can be exploited?
Marcel Ströhle: Sure. One example is the exploitation of unprotected interfaces. For instance, if a developer forgets to disable a debug interface, it can provide root access to an attacker. Connectivity options like USB, Ethernet, and PCI Express can also be attack vectors. There's also the issue of physical manipulation, such as using a laser to trick a MEMS microphone into hearing non-existent commands or exploiting rowhammer techniques in memory to manipulate data.
Scott Williams: That's quite concerning. How can such vulnerabilities impact everyday devices?
Marcel Ströhle: Even everyday devices like wireless keyboards can be exploited. For example, an oscilloscope can decode keystrokes from the wireless signal, or sound analysis can detect which key was pressed based on resonance. Similarly, smart speakers can be tricked into executing commands through light manipulation of their MEMS microphones.
Scott Williams: That's fascinating and a bit scary. What drives people to exploit these vulnerabilities? Is it just because they can?
Marcel Ströhle: In the information age, control over data and systems is incredibly powerful. The motivations can range from financial gain to political influence. For instance, I recently learned that North Korea funds much of its operations through cryptocurrency obtained via internet exploitation by trained hackers.
Scott Williams: Interesting.
Marcel Ströhle: Yes, so there's a lot of power in exploiting any access you might come across.
Scott Williams: I see.
Marcel Ströhle: There's also another layer to it. People might not even have actual access but can still use threats to extort money, claiming they have compromising recordings, for example. Even if only a small percentage falls for it, that's still a significant gain.
Scott Williams: So that explains the effort.
Marcel Ströhle: Yes.
Scott Williams: Okay, where did we leave off?
Marcel Ströhle: Remind me again, which bit?
Scott Williams: The question was, "Why should we also be concerned about the security of hardware components?"
Marcel Ströhle: Ah, yes. To circle back, hardware cybersecurity is crucial because hardware is the basis for everything else. Is your access to the hardware restricted? Is the hardware itself secure? Do you trust everyone who has access to it? These are complexities that we often overlook.
Scott Williams: Okay.
Marcel Ströhle: So, these are just a few points.
"Hardware cybersecurity is crucial because hardware is the basis for everything else."
Scott Williams: All right, let's go on to question three. Marcel, can you walk our listeners through a few real-life scenarios to illustrate the importance of hardware cybersecurity? For example, can you tell us about incidents where compromised hardware led to disastrous consequences?
Marcel Ströhle: One that comes to mind is Stuxnet. It was used to severely damage Iranian efforts to enrich nuclear material. As the story goes, an employee found a USB stick in the parking lot and plugged it into his computer. Unbeknownst to him, it used several unknown exploits to get into the system and caused the centrifuges to fail and destroy themselves.
Scott Williams: Clearly, that was a significant event.
Marcel Ströhle: Yes, it happened over a decade ago, but it's a very good example of how such threats create awareness. In those times, cybersecurity wasn't as prominent a concern. Now, system designers must think about these possibilities because employees need to be aware of the consequences of using unknown devices.
Scott Williams: But it still plays a key role.
Marcel Ströhle: Yes. The whole process needs to be scrutinized. The Stuxnet example shows that internal network access must be restricted. Employees shouldn't be able to access critical parts of the infrastructure easily.
Scott Williams: And speaking of programming hardware, there's a lot of overlap between hardware and software, correct?
Marcel Ströhle: Absolutely. There's a huge gray area because most chips with any complexity involve some level of programming or firmware. For instance, application-specific integrated circuits (ASICs) are hardware but are created by programming chips in a certain way. Once produced, they can't be reprogrammed, but any bugs in the original design will persist.
Scott Williams: So, experts approach this differentiation with a focus on functionality and potential vulnerabilities?
Marcel Ströhle: Yeah
"Regularly review your security implementation and keep your vulnerability management up to date!"
Scott Williams: Okay. So, I assume that for most people, the distinction between hardware and software is based on whether it's something tangible. Marcel, how do experts approach this differentiation? Additionally, there's the aspect of firmware, correct?
Marcel Ströhle: Yeah.
Scott Williams: Could you elaborate on when we specifically refer to firmware and when we refer to software?
Marcel Ströhle: Sure. It’s a gradient. It starts with application-specific chips, which are strictly hardware. They are created by programming the chips in a certain way and then fixing the hardware. Once produced, these chips don’t need further programming, but any software bugs present during their creation will remain in them. So, even though it’s hardware, it can have software bugs if you look at it that way.
Scott Williams: Okay. And so all of that would be found on the hardware chip?
Marcel Ströhle: Yes, those chips are designed to implement specific functions. For example, a light controller with an infrared remote might use application-specific integrated circuits (ASICs) because they are cheap to produce once the functionality is defined. However, with complexity, there's a risk of introducing bugs.
Scott Williams: Okay.
Marcel Ströhle: So they're super efficient and fast, but they can still have software-like problems. After that, there are microcontrollers and related chips like field-programmable gate arrays (FPGAs) that are hardware-adjacent but use firmware to define their function.
Scott Williams: Okay.
Marcel Ströhle: Firmware in this context generally means it's attached to a specific chip, like the processor itself, and has memory on board that defines its functionality. It's not supposed to change regularly, so we refer to it as firmware. Software, on the other hand, is not specifically attached to a chip and might be on a hard disk or solid-state drive. It runs from the CPU and includes the operating system and applications. You could move the hard drive to a different computer, and it would work the same.
Scott Williams: Very good. Well, thank you for that. So all in all, it sounds as if hardware vulnerabilities need to be taken seriously since they can affect industries and individuals. What steps can companies take to mitigate these risks, especially considering your significant involvement in the development of our newest hardware addition, MBX2? Could you comment on that?
Marcel Ströhle: Yeah, there's a whole list of things that need to be implemented correctly. It’s a chain, and every step needs to work, like a chain of dominoes. If one is missing, it fails. That's even outside the company; you need to trust your supply chain. There are factors that help, like using a trusted platform module to verify that only your own signed software will run. Ultimately, if someone has enough resources and motivation, they can introduce security vulnerabilities if they get into your supply chain. Of course, the hardware is next. For example, we worked with Intel to fix an issue with oversized packets in the Ethernet driver, which would cause the system to become unresponsive. It's fixed in the latest kernel now.
Scott Williams: Okay.
Marcel Ströhle: Aside from that, choose components wisely, like error-correcting memory, and ensure everything has good margins for stability. Small power fluctuations shouldn't cause it to freeze or reset.
Scott Williams: Okay. Why develop a new device then? What are the largest challenges and what's new?
Marcel Ströhle: As I mentioned earlier, we collected a lot of feedback and ideas over the years. MBX1 came out in 2018, and that’s a long time in computer hardware. The hardware has progressed to become faster and more efficient. We’ve also had inputs from customers that we could incorporate. For example, we now have modular SFP ports for station connections where you can plug in an RJ45 connector or use fiber optic connections in any configuration. This flexibility is useful for service providers who need different configurations for different customer substations.
Scott Williams: Okay.
Marcel Ströhle: Another improvement is the enhanced performance from new components, faster hard disk, more RAM, and more efficient processes. We’ve also made it possible to mount the device on a DIN rail for easier installation in substations.
Scott Williams: Help me here. For a layperson not familiar with the terminology, what is a DIN rail?
Marcel Ströhle: A DIN rail, also called a top hat rail, is a metal rail with a specific profile used to mount devices in racks in substations for permanent installation.
Scott Williams: Okay. Very good.
Marcel Ströhle: The largest challenge was the housing. We had to fit the CPU module and SFP modules into the existing size of the device, which left almost no space. We managed it by picking the right components. Additionally, going through all the testing and certifications was a major effort, ensuring the device works perfectly in various conditions and complies with regulations in different countries.
Scott Williams: Sure. So you're really trying to stay on top of things the whole time, not only about your continued development but also the development of the components you need and other types of standards influencing the process. Is that correct?
Marcel Ströhle: Yeah, we follow industry-relevant standards that customers want to reference. They need to know our new device will meet their requirements without interfering with other systems.
"The most important thing is to not focus too much on one specific area, like hardware or software cybersecurity. The entire chain is important—from physical access to the hardware, to the firmware and software running on it."
Scott Williams: Okay. So, Marcel, you mentioned that the MBX is designed to withstand sophisticated attacks. Could you give our listeners some insights into how it achieves this level of security?
Marcel Ströhle: Yeah. On the hardware side, we examined all the available interfaces I mentioned earlier. If an interface isn't used, we disable it in the BIOS. For example, I²C, SPI, and serial interfaces—all these are present on the CPU and the CPU module for debugging purposes or interfacing extra components. Like on your laptop, there's stuff used for low-level functions like the display. We review all of that, and if it's not needed, we disable it. We also choose the right components, like industrial-grade CPUs and error-checking memory. Our system disk has powerful power loss protection. We stay updated on security updates relevant to our components.
Scott Williams: Okay.
Marcel Ströhle: We designed our system with significant performance headroom, which sets us apart from others who use smaller processors and central analysis. But don’t quote me on that too much as I’m not deeply into that area.
Scott Williams: Considering the future of hardware cybersecurity, what trends and technologies are shaping the future, and how can organizations stay ahead?
Marcel Ströhle: One emerging technology is quantum computing. Many are researching its implications for security and how to maintain secure communication in a future with ubiquitous quantum computing, which is still in the experimental stage.
Scott Williams: Could you describe what quantum computing means?
Marcel Ströhle: Not in too much detail, but it’s a new paradigm in computing that uses quantum effects to perform many calculations in parallel.
Scott Williams: Is this similar to artificial intelligence?
Marcel Ströhle: Not directly related. One might enable the other to achieve significant advancements, but we’ll see.
Scott Williams: Okay.
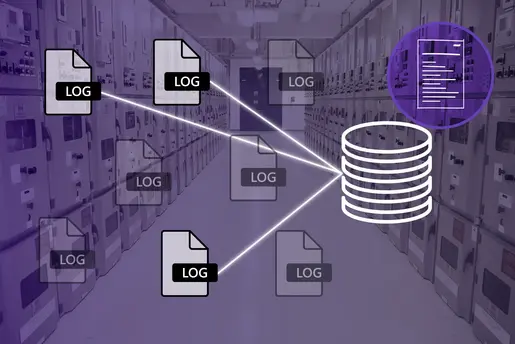
Marcel Ströhle: To stay ahead of the curve, regularly review your security implementation and keep your vulnerability management up to date. Secure crypto processors in your infrastructure can be very helpful. For example, to access our devices, we generate a unique certificate for each device that’s valid for a limited time. Without the crypto processor, we would just have a password or an SSH key, so now security is more dynamic. To hack into our devices, one would need to understand this crypto system and generate that certificate.
Scott Williams: Interesting. So, as we wrap up our conversation, Marcel, what key takeaway would you like our listeners to remember about the critical role of hardware cybersecurity?
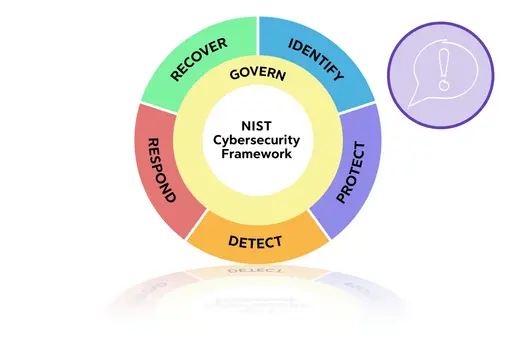
Marcel Ströhle: The most important thing is to not focus too much on one specific area, like hardware or software cybersecurity. The entire chain is important—from physical access to the hardware, to the firmware and software running on it. Consistency in your security principles is crucial. If you have two-factor authentication for your software, don’t leave your computers unlocked. Make sure you can trust your supply chain. Working with third parties can also help, like when we collaborated with the German Federal Office for Cybersecurity to certify our StationGuard on RBX1.
Scott Williams: Okay, super. Thank you, Marcel, for joining me on this episode of Energy Talks and sharing your expertise and insights on hardware cybersecurity. It’s been an enlightening discussion.
Marcel Ströhle: Thank you, Scott. I really enjoyed our talk. My last piece of advice for all the listeners is: stay vigilant, stay secure, and keep those firewalls up.
Scott Williams: Good points to remember. Thank you, Marcel.
Marcel Ströhle: Thank you.
Listen to our podcast