Cybersecurity for Industrial Power
Supplier
You are the driving force behind the stability of global markets – and we are here to protect you!
65%
of industry organizations lack cyber risk mitigation policies for service providers.
(Source: OMICRON, 2023)
15+
external IP addresses have full access in the station bus on average.
(Source: OMICRON, 2023)
3,5M
cost of an average cyber attack.
(Source: Ponemon Institute, 2018)
Challenges of the
Industrial Power Supply Security
Your company is critical to securing the power supply of industrial plants and vital to powering countless businesses. However, the challenges of protecting your assets from cyber threats are often underestimated, which can result in devastating consequences. Limited resources, varying expertise among the team, and competing priorities – we understand your unique challenges and the importance of protecting your business assets. A successful cyber attack could have catastrophic consequences, disrupting the economy and risking lives.


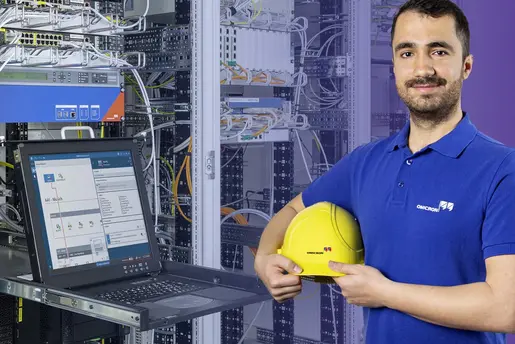
“We support you with resource bottlenecks in your control center through real-time detection and reporting of cyber attacks, automated vulnerability management and a very low false positive rate.”
Christoph Rheinberger
Cybersecurity AnalystIdentify and Respond to Threats
in Industrial Networks
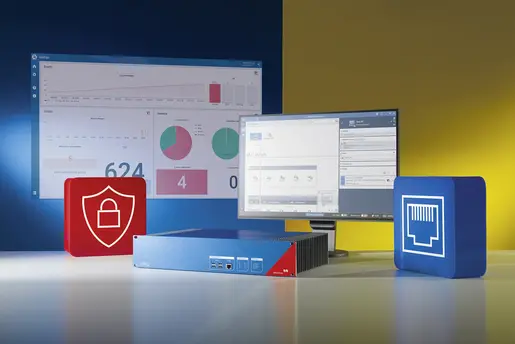
Our comprehensive security solutions are specifically designed to address the challenges of protecting your power supply assets.
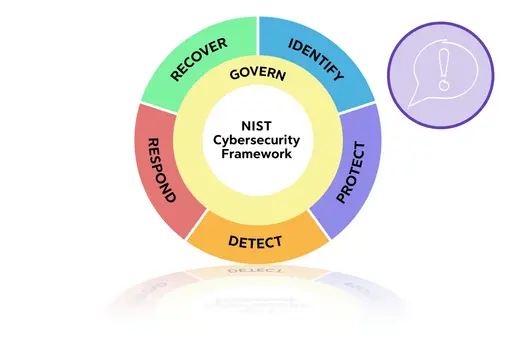
We provide a deep understanding of the aspects and risks involved. Our security assessments, functional monitoring, IDS, and vulnerability management minimize your system's risk factors and increase your SOC's efficiency by reducing false positives, while our audit preparation and defense support ensure that you are always prepared for any potential security events. You can effortlessly increase the efficiency of your SOC by minimizing false positives.
With our help, you can focus on what you do best - powering the economy and driving growth by ensuring the power supply of critical industry processes or data centers.
Security Risk Assessment
How cybersecure are your assets?
Protect your OT power networks and get:
- a comprehensive report,
- actionable recommendations, and
- ongoing support.
Intrusion Detection – Easy Handling, High Efficiency
We emphasize the security of your power grid components, including visibility, DPI, and advisories, to guide analysts in investigating potential incidents. You can rest assured that your critical infrastructure is protected from cyber threats.
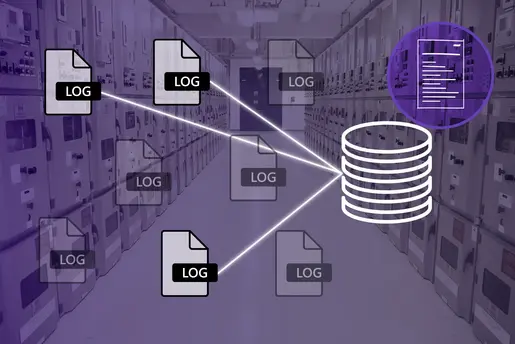
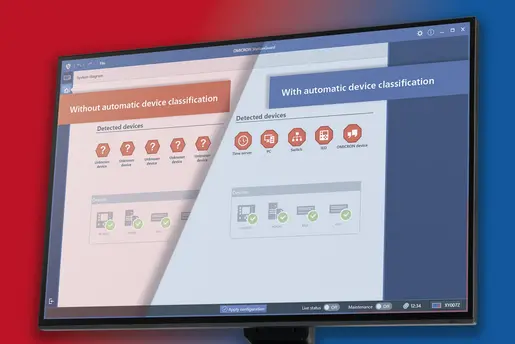
Asset Inventory for High-Security Posture
How much do you really know about your assets and their firmware version? Use our solution to streamline the process of identifying and managing assets down to the bit, enabling detailed and efficient risk assessment.
Prioritize and Protect with Ease
Our vulnerability management system reduces risk and vulnerabilities, so you can prioritize effectively. We have you covered with audit support, IDS checklist, training, and SOC/SIEM integration.
Resources
Contact Us!
We’re looking forward to helping you.
- Have a question?
- Need more information?
- Would you like to request a demo?